From Autonomy to Accountability: Managing Agentic AI Risks
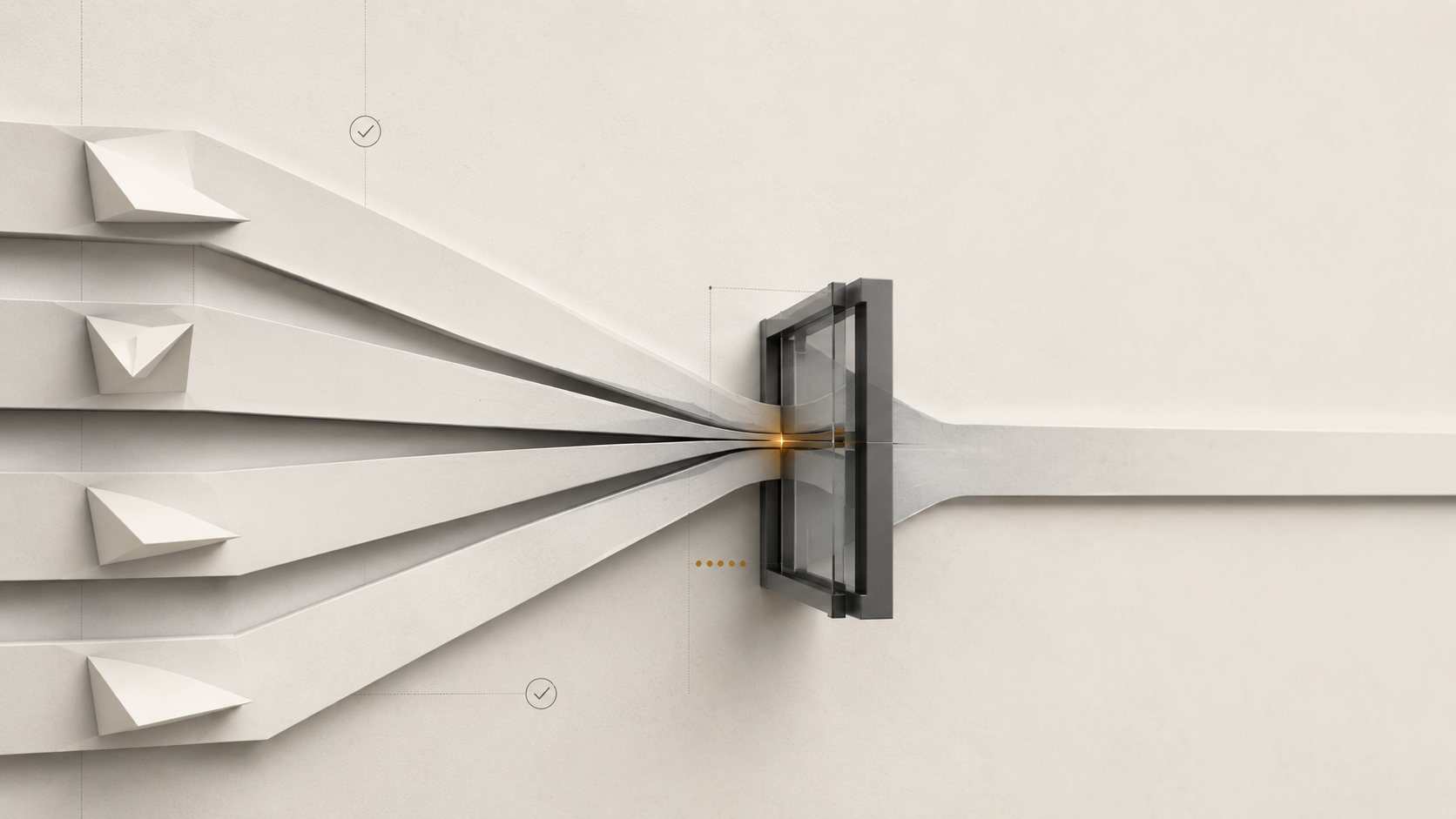
Agentic AI shifts automation from single-task models to autonomous decision-makers, amplifying risks of misalignment, bias, and data leakage. OWASP’s new guidance equips SMEs with lifecycle security practices, ensuring governance, transparency, and resilience as autonomous agents move from experimentation into production. IT leaders and CISOs should read this article to learn how to secure agentic AI in production using OWASP’s guidance.